Solutions
Networking
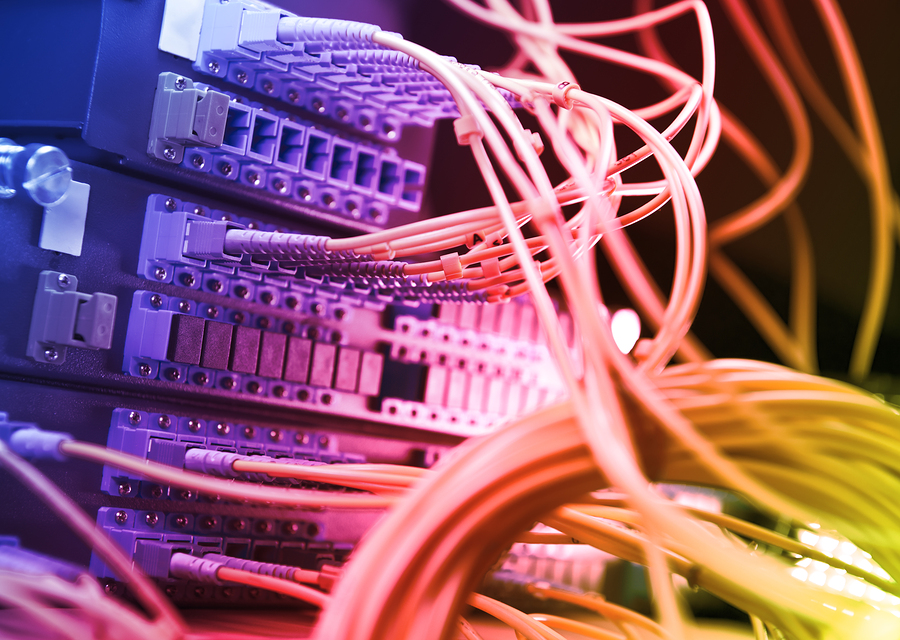
We create exceptional network infrastructures with a portfolio of best-of-breed products, holistic network knowledge, and intimate understanding of security needs.

Mobility
Today’s mobility requirements outpace the infrastructure supporting new bandwidth-hungry apps and low-latency voice applications. Our wireless solutions are tailored for your unique density and application needs.

Security
Our approach to security takes in to consideration the client’s industry, current threats, existing enterprise architecture, and personnel skills for a tailored security program.

By Industry
Our teams are trained in the unique technical and procurement requirements for major industry segments, and we offer packaged offerings tailored to the security and environmental needs of each.
Why Choose Carolina Advanced Digital, INC?
Latest News From Our Blog
Read about what we’re doing, what others are saying about Carolina Advanced Digital, and where you can find us.
Our Partners
Click below to learn more about our partners and their products.





























